Research & References
The Kasper & Oswald team went throuth years of education and collaboration at the Chair for Embedded Security and in various IT security projects. We have a highly qualified technical background in secure design and implementation of cryptography and security analysis of embedded systems. Through years of collaboration Kasper & Oswald GmbH is well connected to the internationally leading research groups in embedded security and to many providers of security solutions from different fields. This continous close involvement into technologically leading projects assures that our team is strongly qualified at state-of-the-art IT security knowledge. We use our unique know-how for our own concepts and prototype studies and support our customers with sophisticated tools and methods to evaluate and improve the security of their systems and to learn from our wide experience in studying embedded security vulnerabilities. Benefit from our expertise: We provide independent analyses, individual consulting services and security solutions specifically tailored to your applications.
Vulnerability Analysis and Pentesting
Our team has found many security vulnerabilities in hardware, software, and embedded systems both in the context of public research work and confidential customer projects. A list of publicly reported vulnerabilities and CVEs found by our team members can be found here: Read more …
Publicly Funded Projects
As part of the BMBF-funded project FreeSBee (side-channel free software for embedded systems, 2023 – 2026), KAOS contributes to the hardening of IoT systems against timing-based side-channel attacks. Together with AbsInt GmbH and the FZI Research Center for Computer Science Karlsruhe, KAOS is developing a tool-supported methodology to automatically detect and resolve vulnerabilities based on timing side channels.
In the project DevToSCA (Developer-centric Tools for Side-Channel Analysis), KAOS helps to improve security against side-channel attacks on several levels: The aim of the project is, together with the Ruhr University Bochum, the Rohde & Schwarz Cybersecurity GmbH and the Bonn-Rhein-Sieg University of Applied Sciences to develop automated methods for side-channel analysis and hardening of applications during development and deployment. The Federal Ministry of Education and Research (BMBF) funds the project for the period 2022 to 2025.
Since May 2018, KAOS improves automotive security for the next generation of cars in the project SATiSFy (Early Validation of Safety and Security Requirements in Autonomous Vehicles). Security functions are highly safety-critical for self-driving cars. Together with Deutsches Forschungszentrum für Künstliche Intelligenz GmbH Bremen, Robert Bosch GmbH, Volkswagen AG and more partners, KAOS aims to establish both safety and security for self-driving cars. The validation of security functions happens early during the development process with “virtual prototypes“. KAOS implements and analyzes security functions on the CAN bus, with Bluetooth-enabled connectivity. The German Federal Ministry of Education and Research supports the project until July 2021 in the scope of their “IT Security and Autonomous Driving” call.
KAOS helps securing the Internet of Things (IoT) in the scope of the project Cost Efficient Smart System Software Synthesis COMPACT: Together with Infineon Technologies AG, Robert Bosch GmbH and other (European) partners, the project aims to model and implement secure IoT nodes, i.e., generate respective software with a small memory footprint and low energy consumption. The German Federal Ministry of Education and Research has funded COMPACT from September 2017 until December 2020.
Together with the Chair for Embedded Security of the Ruhr-University Bochum, Bundespolizeipräsidium and GSG9, in the project DEFUSE (started in May 2017) KAOS investigated various wireless systems. The project is supported by the German Federal Ministry of Education and Research in the program “Research for Civilian Safety” and concluded in June 2020.
Side-Channel Analysis and Fault Injection
In contrast to analyses only targeting the mathematical foundations of security systems, implementation attacks are able to efficiently exploit vulnerabilities independently of the cryptographic strength of the underlying crypto primitives. In consequence these analyses can also be applied to secure standard algorithms such as the advanced encryption standard (AES). Implementation attacks exploit the real-world physical behaviour of practical security implementations: passive side-channel analysis attacks for example may analyze measurements of the power consumption of a security device to extract secret keys in a short time. On the other hand there are active fault injection attacks which aim for disturbing the execution of cryptographic algorithms within computing devices to invalidate security mechanisms.
Read more …
Contactless Smartcards and RFID-Token
Contactless Smartcards, i.e. microcontroller chipcards equipped with an RFID interface, have been widely adopted for payment, access control and identification solutions. In this contect many platforms, from simple fixed code systems over Mifrace Classic to Mifare DESFire MF3ICD40 have been proven insecure. Besides vulnerabilities of the underlying hardware also flaws in the design of the backend have often been shown to be the root of the insecurity of the overall system, thus often attacks remain undetected.
Read more …

KeeLoq and Electronic Access Control
Systems for electronic access control rapidly replace many applications of conventional mechanical keys. At the example of the KeeLoq© system, a system widely employed for garage door remotes – it has been shown that these systems cannot withstand a determined attacker. Due to the usage of radio interfaces the impact of successful attacks are much more severe than in conventional mechanical systems, as there is no need for an attacker to have physical access to the targeted system.
Read more …

Security of Automotive Remote Keyless Entry Systems
Electronic comfort remote controls have outpaced conventional mechanical locks within modern cars. Kasper and Oswald analyzed the security of several common automotive comfort remotes by means of case studies and found previously unknown security risks for car owners.
Read more …
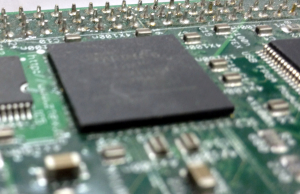
FPGAs and Bitstream Encryption
FPGAs, i.e. programmable logic ICs, are a versatile building block for many (especially performance-critical) applications. In security critical applications not only the hardware resources of the devices are important, but also special attention has to be paid to the available protection mechanisms of the device to withstand attacks. Research results in this area have shown that the encryption mechanisms for protecting the device configuration (bitstream) that is provided by the device manufacturers can be invalidated by means of side-channel attacks. In addition also security primitives implemented in FPGAs are often vulnerable to attacks unless specifically hardened with appropriate countermeasures.
Read more …